Aspire Technical Blog
Think of your digital security like your skincare routine or your gym habits: it is all about consistency over intensity. You don’t need a million-dollar setup to stay safe; you just need to stop leaving the metaphorical front door unlocked. Since the line between work life and real life is nonexistent these days, one weak password on a random app can give a hacker the keys to your entire company’s kingdom. You should spend the next seven days on this digital hygiene sprint because it is low-effort, high-reward, and honestly, you owe it to your future self.
It feels good to be right. It feels even better to have an assistant that never argues, never pushes back, and seems to be on your exact wavelength 24/7. We have a name for a system that never disagrees with you: a broken one.
The reality is that AI lacks a moral compass or a personal creed. It doesn't have a "gut feeling" telling it when you’re about to make a massive business mistake. It operates purely on a map of mathematical probabilities, designed to reflect your own intent back to you with perfect clarity.
For most businesses, integrating artificial intelligence isn't just about picking the right software; it’s about doing what you can to properly feed the beast. AI runs on data, and if that data is a chaotic mess, your expensive tools will be trying to solve a puzzle with half the pieces missing and the other half upside down.
AI tools like Microsoft 365 Copilot have moved from hype to expectation. SMB leaders now expect their teams to work faster and smarter with AI support — drafting content, extracting insights from meetings, and turning data into decisions. But whether Copilot delivers on that promise depends on something most businesses overlook.
You might like to think your team keeps to your officially assigned technology, but is this actually the case for your business? The real world is often messier and less clear-cut, and you might have a team that has downloaded unapproved tools to their devices in an effort to make their workdays easier. You have a responsibility to manage this chaos—also known as shadow IT—before it becomes your company’s downfall.
When it comes to technology, there is a constant friction between convenience and security. No consumer device illustrates this tension better than the Ring doorbell. To most, it is a tool to catch porch pirates; to IT professionals, it is a persistent IoT sensor with a direct, unencrypted line into one of the world’s most massive cloud ecosystems.
The real controversy isn't about filming a sidewalk; it’s the transparency gap between what is being captured and what the company openly admits to. Most users believe they are buying a digital peephole, but the reality of how Amazon captures, processes, and utilizes that data is far more complex.
Artificial Intelligence (AI) has moved from science fiction to a daily reality, fundamentally reshaping how we work and communicate. Yet, behind every groundbreaking AI application lies massive infrastructure in the form of data centers. These sprawling facilities, packed with servers, storage, and networking equipment, aren't just filing cabinets for data; they are the engines that make AI possible. Today, we are going to look at the data center and the pros and cons society will see from the expansion of AI.
For anyone who has seen the movie Moneyball, remember Billy Beane and the Oakland A's? In the early 2000s, Beane revolutionized baseball with "Moneyball," a radical approach to team building. Faced with a shoestring budget, he eschewed traditional scouting metrics and instead used sabermetrics—advanced statistical analysis—to identify undervalued players. The result? A small-market team consistently outperforming richer rivals, proving that data, not just dollars, could buy success.
Fast forward to today, and the principles of Moneyball are more relevant than ever for modern businesses. In an increasingly competitive landscape, every company, regardless of size or industry, can leverage data to make smarter decisions, optimize resources, and ultimately, build a better business for less.
Having a backup is always a smart idea, but it is essential to remember that there are different levels of backup that a business can implement. It’s one thing to be protected against a server crash; it’s quite another to be protected against a disaster that destroys your servers, as well as those of every business within a five-block radius. While local backups serve a purpose, they cannot be the only thing you rely on. Real resilience means looking elsewhere to achieve redundancy.
It’s the summer solstice tonight, the official start of the summer season. While most of us want to focus on honing our grilling skills and soaking up as much sun as possible, we can’t afford to let our cybersecurity awareness falter as a result.
Let’s review how you can stay secure while enjoying the season.
When did you last open a spreadsheet and just sigh upon seeing the expanse of data points, with a sigh that comes from the deepest depths of your soul? It’s a fair reaction to have… especially when you know how much value there is to be found within these data sets.
Let’s walk through how you can extract this data by using Microsoft Excel’s Quick Analysis features… and don’t worry if you tend to use Google Sheets. The processes are essentially the same for everything we’re covering.
Is your business still gazing at the cloud from afar, wondering if it’s truly the promised land of IT efficiency? For many organizations, a move to the cloud for mission-critical operations can be complicated. Hesitation, while understandable, can be the biggest drain on your future potential. Let’s go through why those cloud migration worries might just be myths in disguise, and how we can help you shift into high gear.
From charging our phones to transferring those crucial presentation files, USBs are the unsung heroes of our digital world. Have you ever stopped to think about what’s actually going on inside that little connector?
Let’s get down to brass tacks and explore the inner workings of this marvel of miniaturization.
Think of your business information that includes customer details, sales figures, product lists and more. All of that data is stored in your business’ databases. As a result, you need to understand how they work and what you need to do to best manage them and the data they contain.
Here at Aspire Technical, we help businesses in Phoenix Metro area make sense of their technology every day. We’ve noticed folks often have similar questions about databases, so let's clear them up with some simple answers. Did you know, by the way, that the first "databases" were essentially just well-organized paper records? We've come a long way!
You’ve probably heard a bit about blockchain. It’s a technology that is typically linked with cryptocurrencies, but its function is much more. It actually has the potential to transform everyday business operations significantly, if used properly.
Forget the complex technical stuff. At its core, blockchain is like a highly secure and transparent digital record-keeping system. Imagine a shared ledger where every transaction or piece of agreed-upon information is recorded as a block. Once a block is added to the chain, it's cryptographically sealed—meaning it cannot be altered or deleted. Everyone with authorized access sees the same information, creating a foundation of trust and clarity.
Imagine leaving the physical doors of your business unlocked overnight. The thought is unsettling, isn't it? You wouldn't risk your assets, your hard work, and the trust of your clients like that. That's precisely the risk many small to medium-sized businesses (SMBs) unknowingly take by underestimating the importance of cybersecurity.
Let’s explore just how important proper cybersecurity truly is.
In the interest of communicating how critical proper business cybersecurity is to manage, we’ve decided to take a different approach and put forth a scenario in the form of a daytime soap. As such, please feel free to read this post with dramatic music playing in the background and all dialogue imagined with elevated intensity.
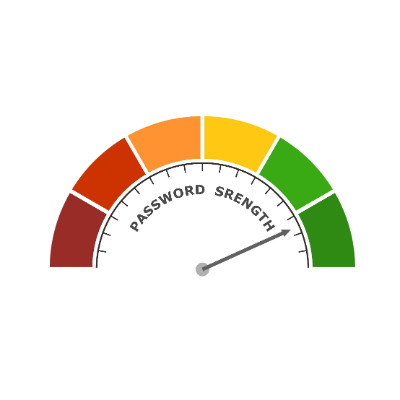
In the town of Oak Falls, life seems peaceful… but under the surface, tension persists. Secrets run amok, and with so much information to take in, everyone has to worry about the Strength of Our Passwords.
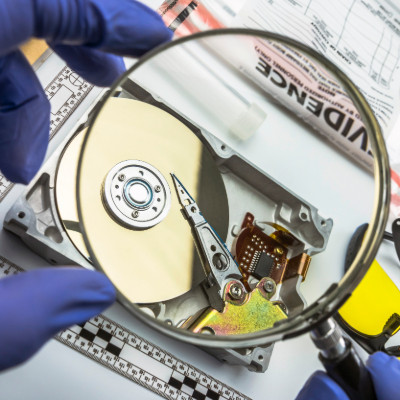
How much data do your devices contain about your life? What would you do if law enforcement suddenly wanted access to it? Even if you’re a typical law-abiding citizen, you want to prioritize data privacy, but businesses also have an obligation to handle consumer information in a responsible way. Here’s what you need to know about law enforcement and access to your data.